With the EU’s General Data Protection Regulation (GDPR) now in effect, GDPR preparedness should be top of mind for businesses everywhere, not just those based in the European Union (EU). This GDPR overview will take you through the basics, including the seven principles that drive regulation and enforcement.
Table of Contents
What Is GDPR Exactly?
Top Questions About GDPR
Deep Dive Into GDPR:
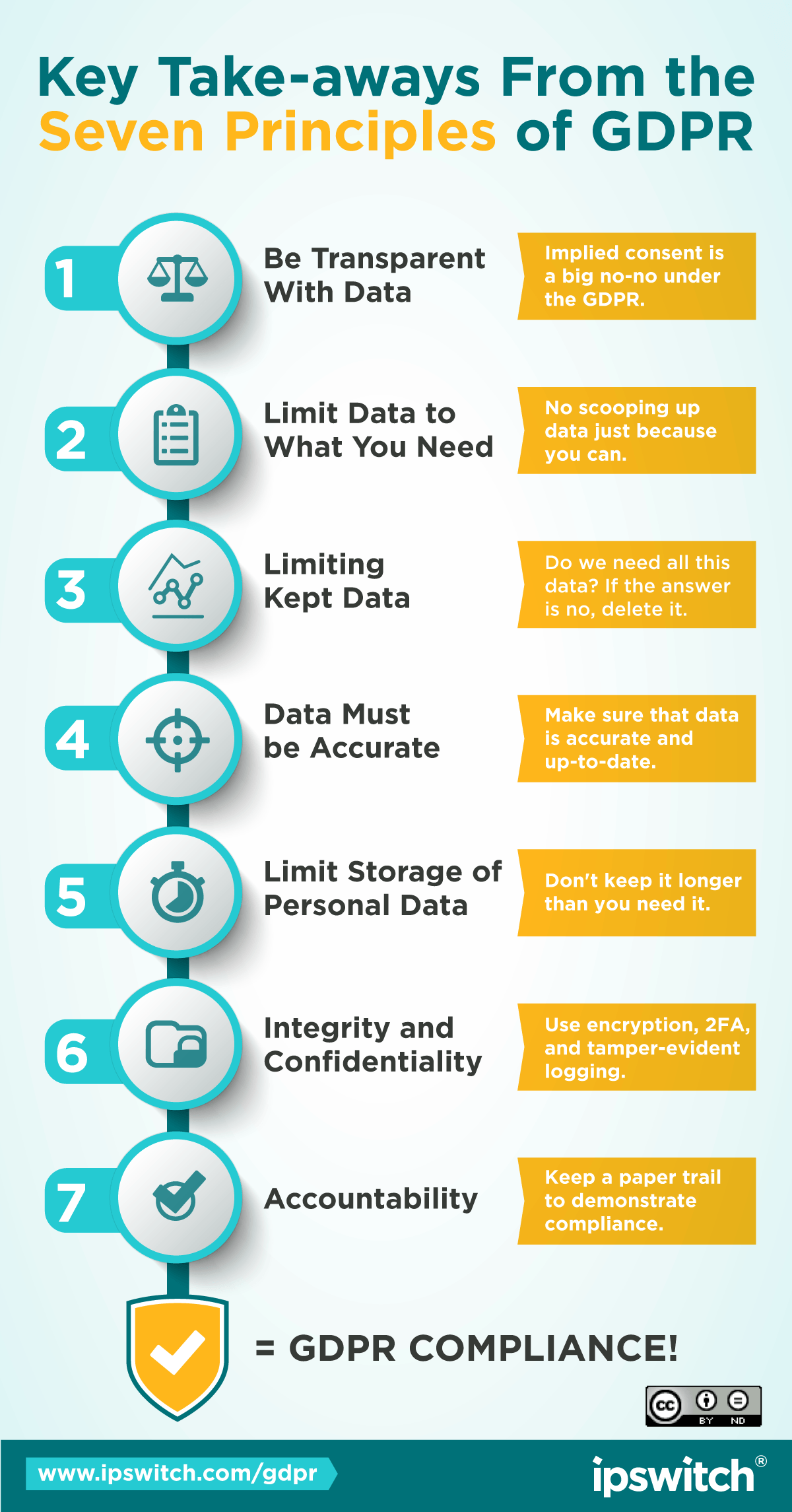
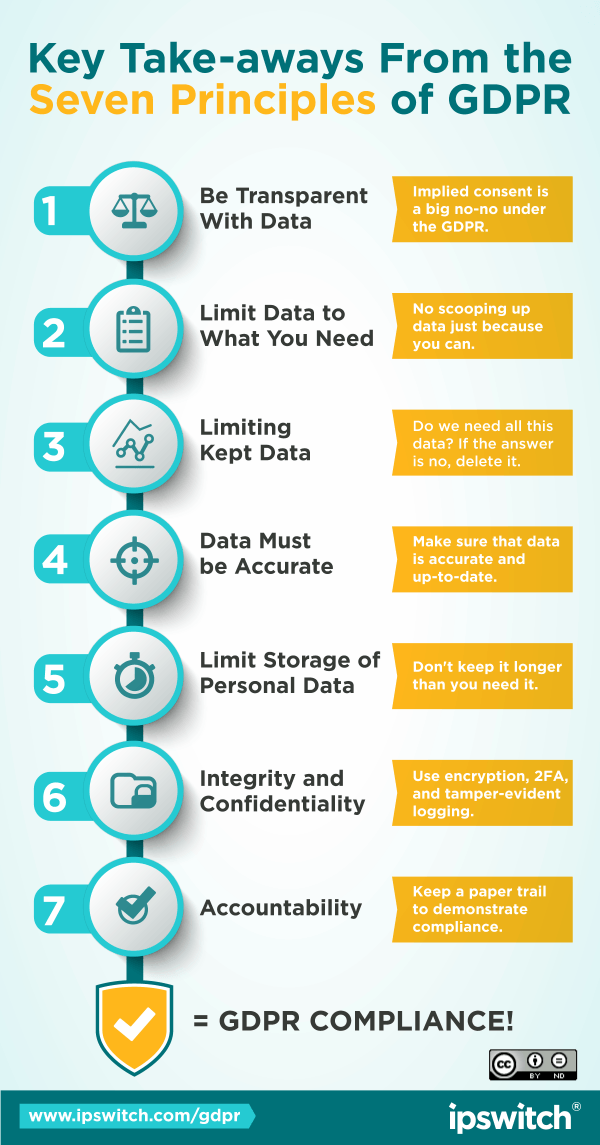
Principle 1: Transparent Processing of Data
Principle 2: Limitation of Collected Data
Principle 3: Minimize Collected and Stored Data
Principle 4: Personal Data Must Be Accurate
Principle 5: Limit Storage of Personal Data
Principle 6: Integrity and Confidentiality
Principle 7: Accountability
What is GDPR, Exactly?
The General Data Protection Regulation (GDPR) is new data protection law for all 28 Member States in the European Union.
GDPR sets a high standard for data protection, and applies to any organization that processes the personal data of EU data subjects, whether that organization itself is based in the EU or not. This is important, because the standards set by GDPR are much more stringent than those set by current U.S. privacy laws. And
the penalties for non-compliance are harsh. Up to USD $24M, or 4% percent of worldwide annual turnover, whichever is higher.
Designed to replace the hodgepodge of data protection regulations and authorities currently applicable in the 28
EU member states, GDPR will create a homogenous regulation that will apply across the EU.
The reform modernizes the principles from the EU's 1995 Data Protection Directive and applies to personal data of EU data subjects from that is processed by what the regulation calls data controller and data processors (more on that later).
Top Questions on GDPR
When did GDPR go into effect?
GDPR was signed into law in April 2016 and went effect on May 25th, 2018. After that date, any organization that collects, stores, or processes the personal data of EU data subjects must comply with the General Data Protection Regulation.
What is Personal Data?
In the EU, personal data is defined as any data which by itself, or when combined with other data that the possessor can likely access, can be used to identify an individual. To a cybercriminal, the collection, processing, and transfer of personal data makes organizations across a large number of industries lucrative targets for phishing, denial of service, ransomware, and advanced persistent threat attacks.
Who is a data subject?
According to EU law, a data subject is any person within EU borders whose personal data has been collected (be they EU citizens, residents, or tourists passing through) for the purposes of offering them good and services within the EU. EU citizens are
also considered data subjects when they are abroad, or doing business with an entity located abroad, when that business seeks to offer goods and services within EU borders.
Example: If a German books a holiday stay in Spain using AirBnB
(a US-based service) then GDPR applies because the room being offered is in Spain, inside the EU. If that same person books a room in Japan, GDPR does not apply, because the service being offered is not within the EU.
Long story short,
GDPR protects the data of persons, but defines its reach by the things bought and sold to the EU.
What are data controllers and data processors?
Controllers and processors are two different types of organizations that GDPR applies to-namely, those that "control" personal data, and those that "process" it. A data processor in GDPR is defined as any organization that collects, processes, stores or transmits personal data of EU data subjects. A data controller is the organization that directs the processor's activities.
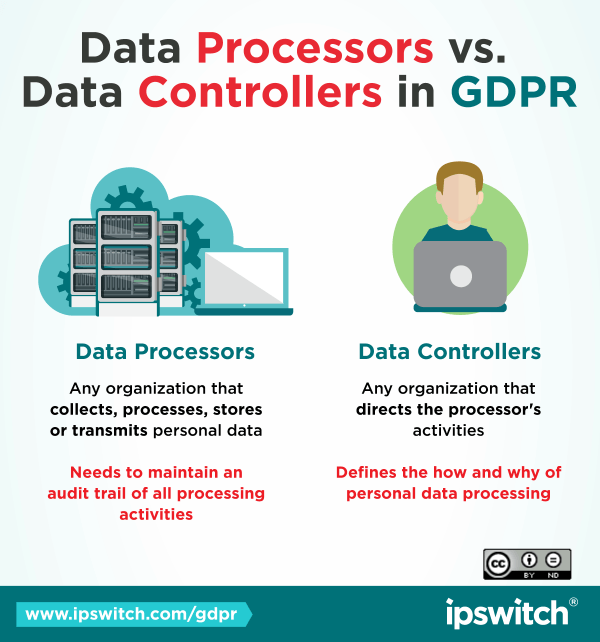
That means the data controller defines the how and why of personal data processing, and the data processor acts on the controller's behalf. For example, a bank that outsources check imaging processes is the data controller, while the outsourcer is the
processor.
Under GDPR, data processors need to maintain an audit trail of all processing activities, but it's the responsibility of the data controller to assure that all of their processors are in compliance. Controllers are not relieved of their
data protection obligations if a breach occurs in a processors network.
Transfers of personal data between controllers and processors must be secure, and the data must be protected while it's processed. In certain cases, GDPR can also require
the data processor to delete personal data that is no longer needed after processing.
Who has to comply with GDPR?
The rules of GDPR apply to any organization that collects, stores or processes the personal data of EU data subjects. It doesn't matter where your company is headquartered. Even companies that do not have a physical presence in the EU must comply with GDPR.
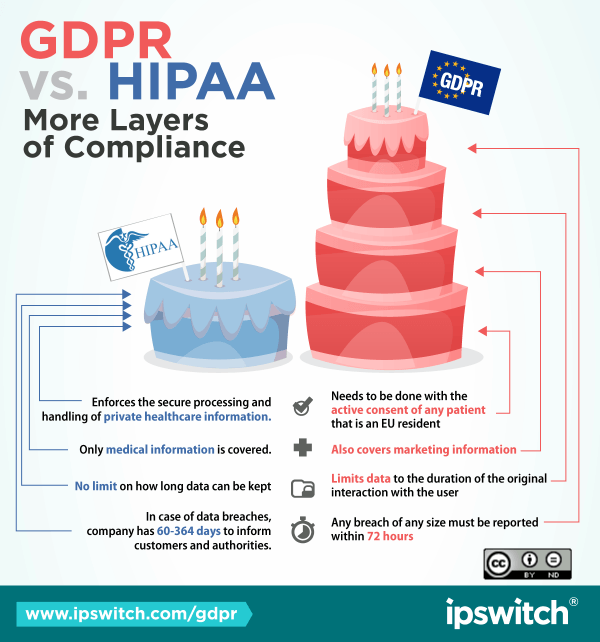
We're already HIPAA compliant - will we be ok for GDPR?
Not exactly. There are some overlaps, but GDPR is a much larger and more far-reaching piece of legislation. You can read more about the differences between the two here.
What are the penalties for non-compliance?
The consequences for non-compliance with GDPR are severe, up to 20 million Euros, or 4% of worldwide annual turnover, whichever amount is higher.
Would Brexit make the UK exempt from GDPR?
No. Even with Brexit, UK firms will have to comply with GDPR. The date for withdrawal from the EU is later than the May 2018 date that GDPR comes into effect. Thus, UK businesses will be under the jurisdiction of the EU and subject to GDPR. After Brexit, UK business will still have to comply if they collect, store, or process the personal data of EU data subjects.
Still have questions?
Check out our Procrastinator's Guide to GDPR for a more in-depth breakdown of GDPR and its implications.
Deep Dive on GDPR Principles
GDPR is built on seven data protection principles that, together, ensure that the rights of the individual are central to the collection and processing of personal data from EU data subjects.
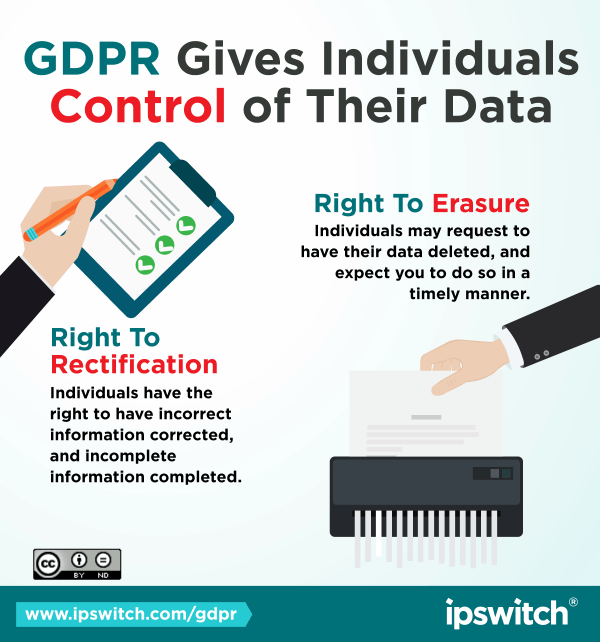
The new regulations strengthen users' control over how personal data is processed and stored, and grants key rights and freedoms such as the right to consent, the right to be informed, the right to data portability, and the right to erasure
of personal data (i.e. the "right to be forgotten.")
Principle One: Fair, Lawful, and Transparent Processing of Data
The first principle of GDPR data protection act is the requirement for "fair, lawful, and transparent processing of data." So what does that mean?
Under this rule, GDPR mandates that a data controller must be capable of providing a data
subject (ie. the user) with detailed information about his or her personal data processing.
To be compliant, this data must be presented in an easily accessible manner, and in clear, concise, and transparent language. In other words,
say goodbye to the 100-page user agreement.
To meet EU requirements for transparency, data controllers must inform individuals:
- Before any personal data is collected
- Whenever any changes in data collection processes are made
- And finally, the data subject must consent to data processing.
This consent can take several forms, but it must be given from a data subjects' own free will, and positive action must be used to indicate consent (i.e. clicking a checkbox). That means implied consent is a big no-no under GDPR.
The law also states that personal data collected and used for processing must be "adequate, relevant and limited to what is necessary for the purposes for which they are processed," and the period for which that data is stored is kept to a "strict minimum."
Principle Two: GDPR Mandates Purpose Limitation of Collected Data
Under the second data protection principle of GDPR [Article 5, clause 1(b)], it’s mandated that personal data from EU data subjects shall be “collected for specified, explicit and legitimate purposes and not further processed in a manner that is incompatible with those purposes.” Any further processing of that data should not be “incompatible with the initial purposes.”
In plain English, this means you need a legitimate, lawful purpose for collecting and processing user data—no more scooping up data wholesale just because you can. If you collect personal data that doesn’t have a specific purpose, you may find yourself out of compliance.
Likewise, under GDPR once you’ve collected and processed data for your purpose, you may not process that data for an unconnected purpose. For example, data collected for research purposes could not be processed and sold for marketing purposes.
Under GDPR, personal data is any data which by itself, or when combined with other data that the possessor can likely access, can be used to identify an individual. That means name, phone number, IP address, email… the whole gamut.
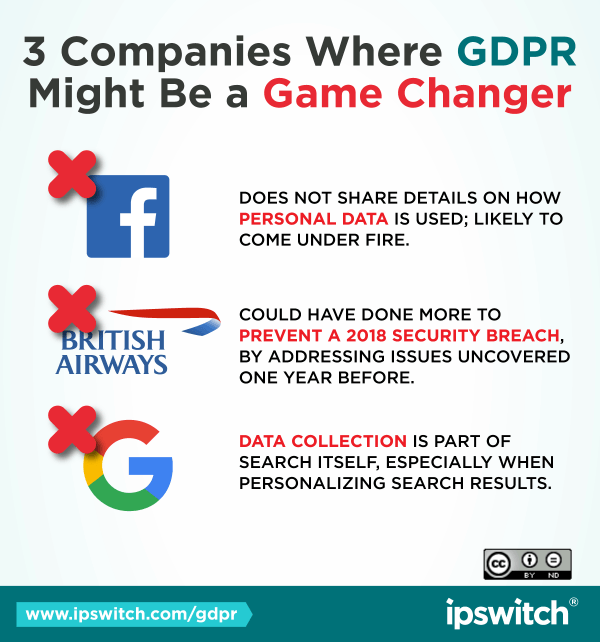
In the recent Facebook scandal, which brought Mark Zuckerberg to testify in front of members of U.S. Congress and the E.U Parliament, it was revealed that British political consulting firm Cambridge Analytica used data collected for research purposes
to target millions of Americans and EU citizens for political advertisements during the 2016 election cycle. Under the new restrictions enforced by GDPR, Cambridge Analytica and Facebook would be subject to hefty fines-up to 4 percent of annual
turnaround, worldwide.
There is currently no such purpose limitation law on the books in the US.
Principle Three: Businesses Must also Minimize Collected and Stored Data
One of the most significant ways GDPR is transforming data collection and processing is the principle of data minimization, under section 5, clause 1(c). According to this principle, all collected personal data must be "adequate, relevant, and limited
to what is necessary in relation to the purposes for which they are processed."
This is closely related to purpose limitation, but differs in that it requires the restriction of which data is stored, as well as the data that is collected.
Essentially, in order to be GDPR-compliant, you must implement data minimization processes and rules at every stage of the data lifecycle-from collection to processing, storing, and use. At every point in the process, you should be asking yourself:
Do we really need this data? If the answer is no, you should delete the information. This process should be documented with a provable audit trail.
Additionally, data minimization means you need to think about how long you intend to
store personal data for. For example, if you need data for a project that will last seven weeks, you must delete that data when the project is finished, and the data is no longer necessary. Currently, it's a common practice to hold on to any and
all personal data in case it may be useful down the road. Be warned: this will not be compliant with GDPR.
In order to stay compliant with GDPR, ask yourself the following questions when collecting data:
- How will I use personal data?
- Can I achieve my goal without collecting personal data?
- How long will I need to keep personal data to achieve my goal?
How MOVEit Can Help You Comply with GDPR Principles Two and Three
If your business collects, stores, processes or transmits the personal data of EU data subjects, the General Data Protection Regulation (GDPR) will apply to you. With this much at stake, the best practice is to assure that the systems, user authentication, and encryption techniques involved in the transmission of personal data are secure and compliant with GDPR. Learn more about how MOVEit can help manage and secure file transfer activity across your network.
Principle Four: Personal Data Must Be Accurate
According to the fourth principle of GDPR, any personal data collected or processed must be "accurate and, where necessary, kept up to date." Furthermore, GDPR mandates that "every reasonable step must be taken to ensure that personal data that are
inaccurate," in regards to the purposes for which they are processed, "are erased or rectified without delay."
So what, exactly, does that mean? In plain English: You can't keep junk data, and it's your responsibility to make sure that
data is accurate and up-to-date. Otherwise, you must erase it.
So say for example you're working on a political campaign, and you're using data from the last election cycle. Under Principle Four it would be your responsibility to ensure
that you are using accurate and up-to-date data before mailing out to those constituents.
This touches on both the subject's right to rectification and their right to erasure-both key provisions of GDPR. Under the right to rectification,
individuals have the right to have incorrect information corrected, and incomplete information completed. Under the right to erasure, they may request to have their personal data deleted, and expect you to do so in a timely manner.
Principle Five: Limit Storage of Personal Data
Remember back in Principle Three, how holding on to personal data just in case it may be useful down the road, won't be compliant with GDPR? Well, the writers of that rule liked it so much that they wrote an entire data protection principle based
on it: the principle of storage limitation.
According to that principle, personal data may not be "kept in a form which permits identification of data subjects for no longer than is necessary for the purposes for which the personal
data are processed." If personal data is to be stored for longer periods, it must be proven that the data will "be processed solely for archiving purposes in the public interest, scientific or historical research purposes or statistical purposes."
Basically, it's just like we said before, you may only keep personal data as long as you need it for the task for which it was collected. The useful life of the data may be far longer, but you may not keep it on, and reuse for other purposes
(or sell it to someone else). This would prevent messy scandals like the one at Facebook/Cambridge Analytica, and is a fundamental right under GDPR.
In order to comply with this principle, you need a policy in place that mandates retention
periods, and documentation requirements for that policy that will let you audit for compliance. You should also frequently review the data that you have, and erase it when it is no longer needed.
Principle Six: Integrity and Confidentiality
Principle Six of GDPR is one of the most important, and for good reason-it's all about security.
Principle Six states that data must be "processed in a manner that ensures appropriate security of the personal data, including protection
against unauthorized or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organizational measures."
In plain English: organizations must treat personally identifiable information
(PII) in a manner that is secure from theft, destruction, or accidental loss. The call for the use of "appropriate technical or organizational measures" is a little fuzzy, and it's likely that GDPR's author were purposefully vague in mandating
security steps, as these technologies and best practices are in a constant state of change.
Without being too specific, the principle nevertheless encourages the use of well established best practices for cybersecurity - things like
encrypting data in transit and at rest, using 2FA, and using tamper-evident logging to track who accesses data.
Principle Seven: Accountability
While Principle Six is the only one that explicitly focuses on security, no GDPR overview would be complete without talking about what everyone is concerned with: consequences.
Principle Seven states, succinctly, that "the controller
shall be responsible for, and able to demonstrate compliance with [the previous principles]."
If you fail to demonstrate compliance with the previous six principles, the consequences can be dire: up to 20 million euros, or 4% percent
of worldwide annual turnover, whichever is higher.
And compliance is mandatory for any organization that collects, stores or processes the personal data of EU data subjects. It doesn't matter where your company is headquartered. Even companies that do not have a physical presence in the EU must comply with GDPR.
But what does compliance look like? How are you supposed to demonstrate compliance? GDPR doesn't
outline how businesses will demonstrate compliance, because that will differ greatly depending on the type of business you do, the personal data you handle, and the size of your organization. But you can bet that you'd better be ready for an audit,
regardless of size. Typical best practices, such as logging of security incidents and access to PII, and internal auditing are recommended.
What's more, it may be advisable to get a risk assessment of our business, which will help you
identify any weak points, and evaluate whether or not you need to improve or implement specific security controls.
Create a GDPR Action Plan
As noted above, if your business collects, stores, processes or transmits the personal data of EU data subjects, the General Data Protection Regulation (GDPR) will apply to you. With this much at stake, the best practice is to assure that the systems, user authentication, and encryption techniques involved in the transmission of files are secure and compliant with GDPR. This GDPR Overview can give you a head start, but your next step should be to discuss GDPR with your internal team and your vendors, to ensure that your company will be ready to do business with EU data subjects.
Learn more about how MOVEit can help manage and secure file transfer activity across your network, improving both security and accountability.