IT Solutions
Managed File Transfer Solutions For Healthcare & Medical Companies
A leading HIPAA-Compliant File Sharing Software
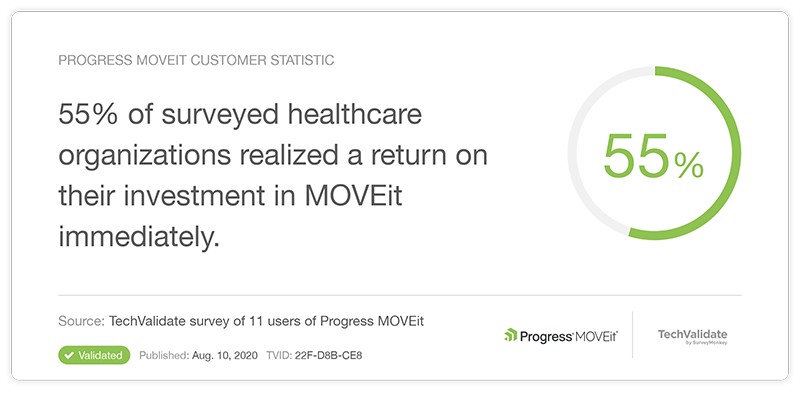
Hundreds of healthcare organizations depend on MOVEit products to deliver scalable, secure and compliant patient care and business services
Security & Compliance
Ensure regulatory compliance in the transfer of PHI
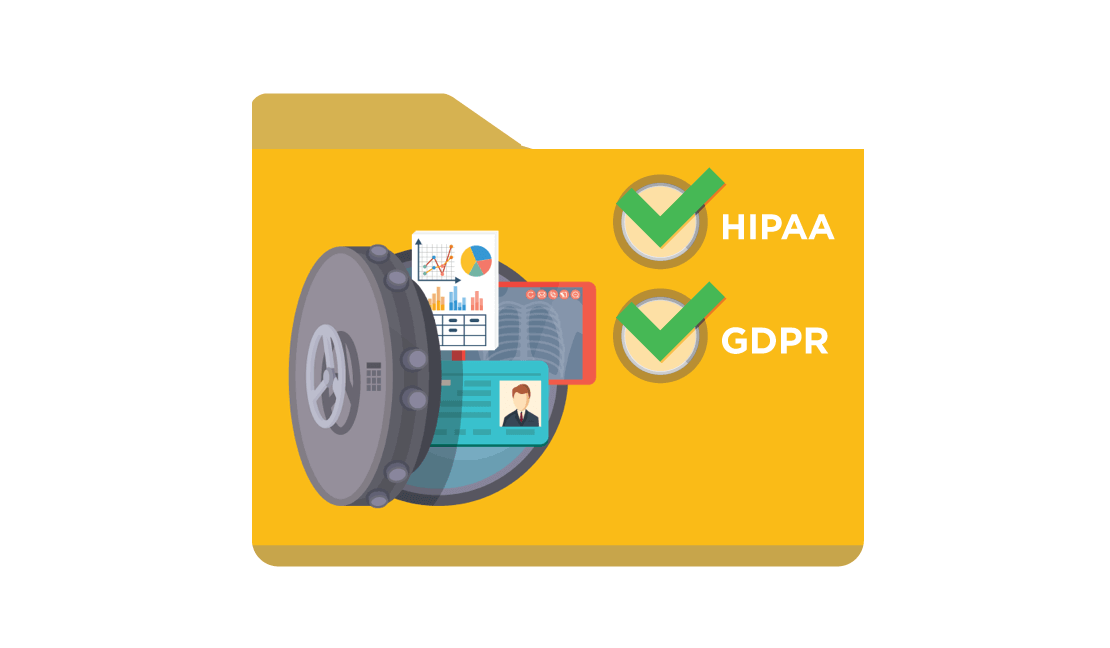
From healthcare billing, to insurance-eligibility inquiries and HCAHPS surveys, the business of healthcare depends on the reliable, secure and compliant transfer of Protected Health Information (PHI). The MOVEit suite of Secure File Transfer products assures encryption of data at rest and in motion, delivery to the intended recipient and detailed audit logs. MOVEit provides the features and deployment flexibility required to meet HIPAA and GDPR compliance.
MOVEit: Secure file transfer for the healthcare sector
IT Operations Efficiency
Meet SLAs, deliver 24x7 services and reduce operations costs
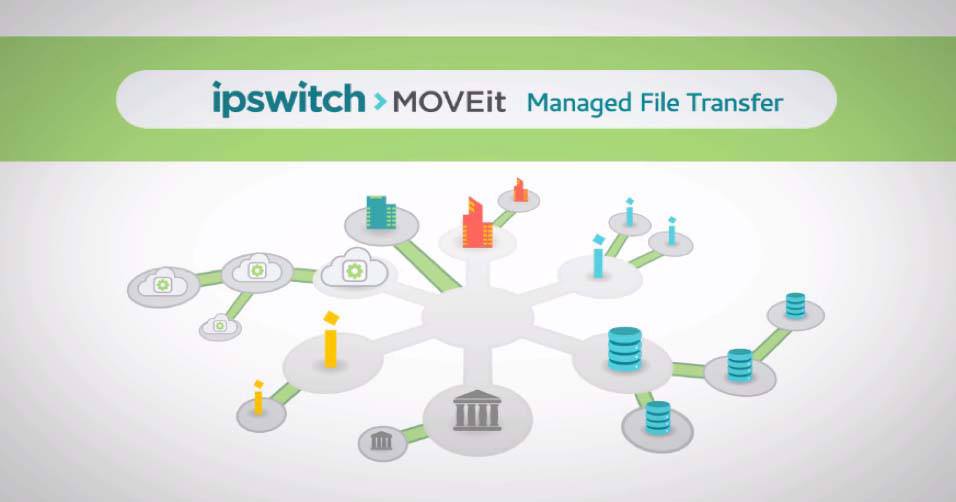
The MOVEit suite of products enables consolidation of disparate file transfer processes under a single management tool with end-to-end visibility, performance reporting and audit trails. It accelerates the development of new services and reduces on-going resource requirements with easy-to-use workflow automation. Its flexible architecture allows you to configure an exact match to your business continuity needs from high-availability to complete failover.
Business Expansion
Drive network growth to provide world-class patient care
Profitable growth of your healthcare network requires on-boarding new healthcare service providers cost-effectively. Scalable IT operations are an essential ingredient for success. MOVEit provides the ideal business service platform to support profitable expansion and the accelerated roll-out of competitive new services such as appointment reminders and patient retrieval of medical records.
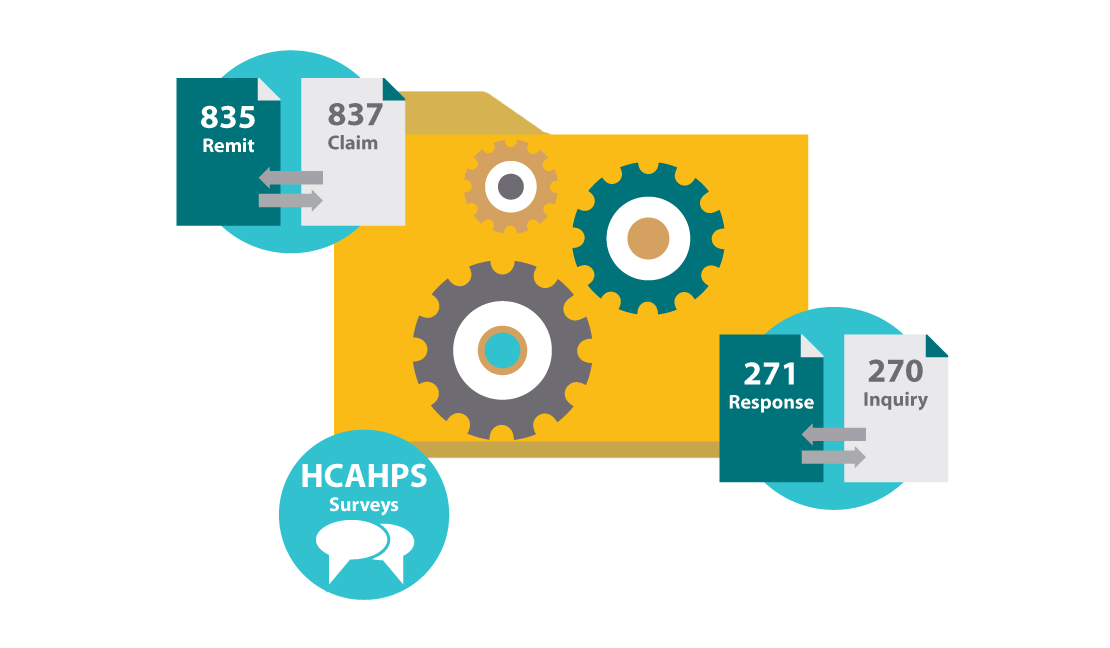
Automate Billing/Payment Processing
Automate your medical billing process and ensure 837 health care claims and 835 electronic remittance advice (ERA) notifications are securely delivered within the time frames required by SLAs and in compliance with HIPAA.
Learn MoreAutomate Patient Survey Processing
Automate the transfer of patient discharge records to survey agencies to ensure that all patient discharge information is securely delivered for appropriate processing and patient survey are conducted on a regular basis.
Learn MoreFeatured Content
MOVEit Secure File Transfer
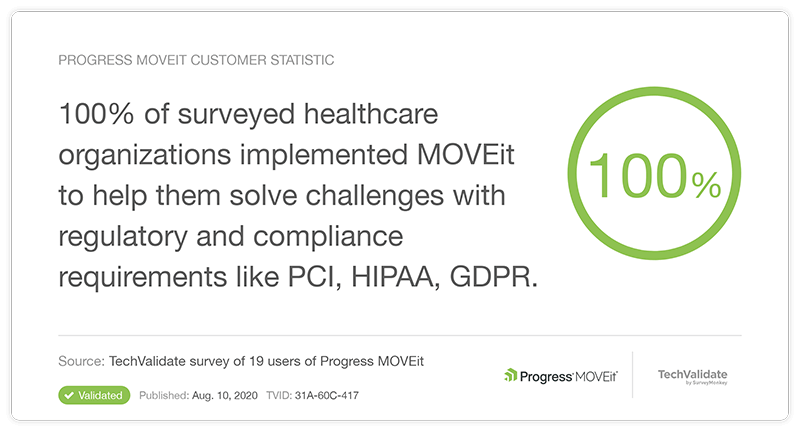
Hundreds of healthcare organizations use MOVEit to assure compliance with data protection regulations like HIPAA and GDPR
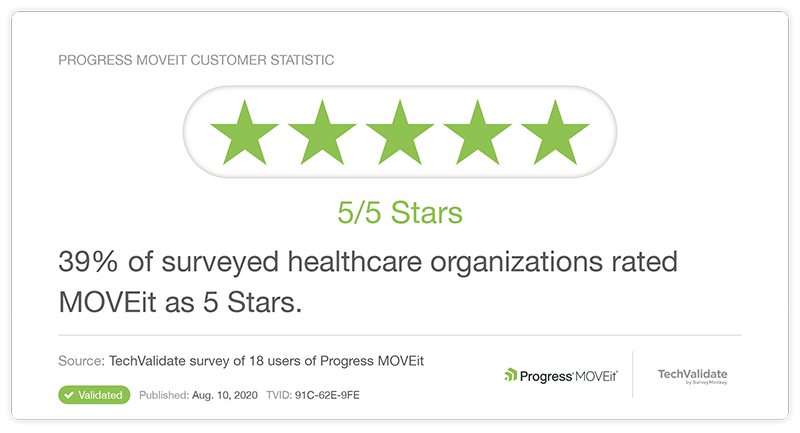
What Our Customers Say