It’s the proverbial 1,000-pound gorilla—a compliance violation. Perhaps you haven’t seen one yet, but you know it’s out there lurking, and it just might come banging on your door any day now.
It’s no wonder many IT teams are scared of the “compliance gorilla,” especially given all the data breaches that have made major headlines in recent years.
Your file transfers are one area in particular that warrant close evaluation as to whether or not they comply with major regulations, such as the General Data Protection Regulation (GDPR). You also want to examine if the way your business executes file transfers creates serious security risks. This includes data transfers that take place internally among your different office locations and externally with your customers and vendors.
Every time end-users send files, the information can be intercepted by a cybercriminal. When the file is received, if it’s not handled properly by your internal systems, personal data or intellectual property could find its way into the wrong hands.
Whether it’s someone with malicious intent or simply someone who should not see the confidential file, it’s something to avoid at all costs. In this blog, we take a look at the security implications of the GDPR, what it takes to avoid the risks of non-compliance, and how a Managed File Transfer solution can help you make sure that “gorilla” does not come banging on your door, in the form of the supervisory authority.
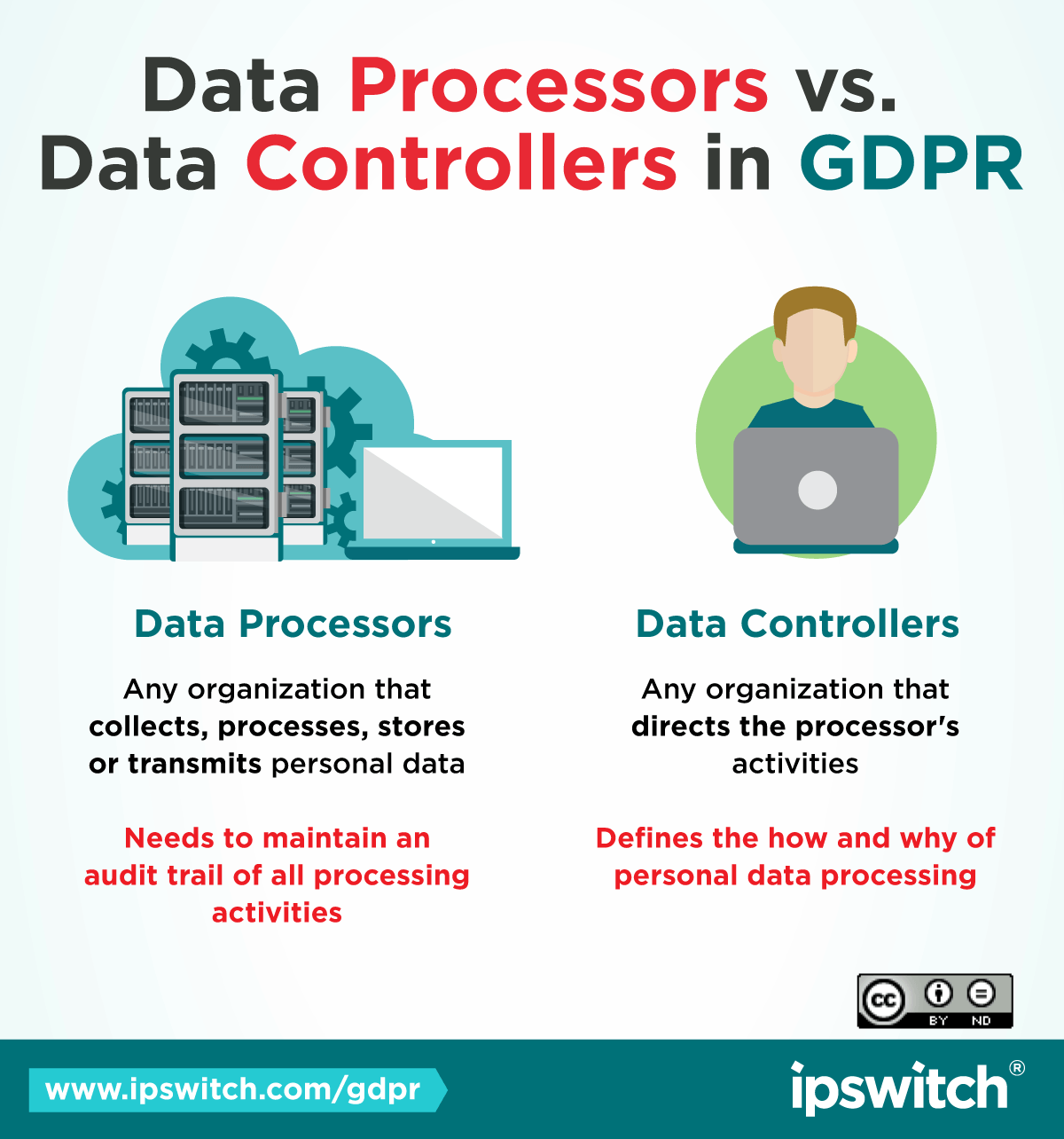
GDPR makes a distinction between companies that handle the data, versus companies that own the data - but the rules apply to both. Learn more about how GDPR impacts the use of personal data.
Why Should Businesses Care About the GDPR?
The GDPR applies to any business that handles private data about residents in the European Union (EU) and the UK, while the UK is still part of the EU. This holds regardless of whether a business is physically located in Europe. Businesses in the U.S. who serve EU residents must also take action to comply.
Even businesses outside the EU need clear consent from EU-based customers to handle their information and applies not only to data gathered after the regulation went into effect this past May, but also data previously collected that is still being stored. All the data and consent documentation have to be audited to ensure compliance with the GDPR standard. Every consent form has to be made available to GDPR commissioners upon request, and businesses suffering a breach must notify the GDPR supervisory authority and any affected customers within 72 hours of the breach occurrence.
Companies that suffer a breach and who are non-compliant face fines. Penalties for non-compiance can run as high as 20 million euros (approximately $23M depending on current exchange rates) or four percent of the offending company’s global turnover, whichever is higher. The amount of the fine will vary depending on the seriousness of the breach.
Given the potential penalties, businesses impacted by the GDPR should take steps now to ensure they know what information they’re holding.
Avoid Risks of Non-Compliant File Transfers
As a starting point to avoid the risks of non-compliance with GDPR, your core file transfer processes should be handled centrally by a small group of managed file transfer servers. If you rely on older file transfer processes, such as basic FTP servers, be aware that they have limitations that expose you to an increased risk of security breaches and non-compliance with GDPR.
For example, your FTP servers may lack SSH or SSL to assure encrypted transmission and authentication. Even more recent file transfer processes such as SFTP and FTPS (which typically provide SSH and SSL) are often lacking when it comes to additional key security criteria—such as automation, visibility, tamper-evident logging, and non-repudiation. Here are some of the issues to be aware of if you are using an older FTP solution:
- Without automation, repetitive file transfer requirements are a cumbersome process, leaving you exposed to the risk of human error resulting in data loss. Automatic file transfer workflows provide a governance mechanism to mitigate the risk of data loss and non-compliance fines.
- FTP servers may also lack the degree of visibility and logging required for compliance certification. The logs should be tamper-evident and keep track of when a file was transferred, if the right party received it, and whether or not it was subsequently deleted.
- Non-repudiation is a must to prove that files uploaded and sent by end-users are identical to files downloaded on the receiving end, whether that be other end-users or external partners. Non-repudiation guarantees the integrity of the data transferred and plays a valuable forensic role if a dispute arises about the file.
Organizations that rely on home-grown scripts to automate file transfers will likely run into scalability issues as well. The complexity of maintaining the scripts can become unwieldy and introduce unanticipated security gaps.
Three Ways Managed File Transfer (MFT) Technology Supports Compliance
As a way to ensure compliance with regulations protecting customer information, Managed File Transfer (MFT) solutions have come onto the market in recent years. MFT can be thought of as one huge centralized file transfer system complete with built-in functions such as visibility, compliance reporting, logging, assured delivery, and tracking.
An MFT solution can also integrate with your existing security architecture features—such as antivirus, data loss prevention, and access control—and provide automatic failover should the system go down.
And your core enterprise applications can run on MFT platforms so that a single implementation can include multiple transfer servers, workflow automation systems, and cloud-based transfer services.
MFT systems also assure data security for business processes that require the exchange of files containing sensitive data with external parties. This makes MFT ideal for compliance with GDPR as well as other protection mandates such as PCI-DSS, HIPAA, and ISO-27001.
Thousands Use MOVEit to Secure File Transfers in Compliance with GDPR
To comply with regulations like GDPR that protect sensitive data, thousands of businesses rely on MOVEit, a Managed File Transfer solution from Ipswitch. MOVEit lets you centrally authorize and trace file transfers, so you know your data is protected at all times. The solution also records transfer data and non-repudiation evidence in tamper-proof audit trails for the amount of time required by regulations and up to the assured destruction date.
We architected MOVEit to integrate with security infrastructures, policies, and applications. With all these features, you gain several key capabilities:
- Ensure no unencrypted data in your perimeter networks (DMZ) and eliminate external access requirements.
- Encrypt files at rest and in motion.
- Provide compliant file transfer access to all users via email, web, mobile apps, or desktop clients.
- Validate encryption and decryption keys are consistent with international legal and regulatory requirements.
- Safeguard the integrity and availability of file transfers at all stages throughout any failures, disasters or outages.
- Failover to assured uninterrupted file transfer processing when necessary.
MOVEit also gives you a choice of authentication mechanisms and supports user-access management, including blacklists and whitelists. To find out more, watch this brief MFT use-case demo to see how easily you can set up fast, secure and high-volume automated file transfers with MOVEit—and make sure that gorilla does not come banging on your door!